Triggers
- Abnormal administrative SharePoint operations that may be associated with malicious activities.
Possible Root Causes
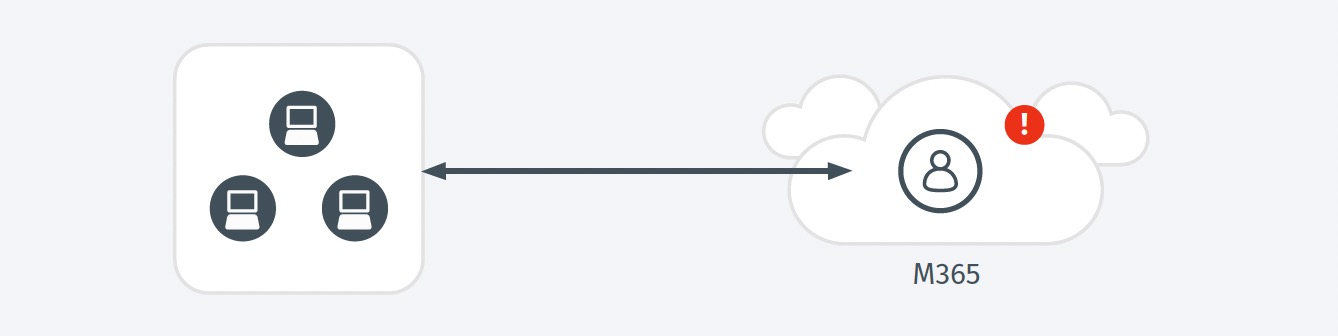
- An attacker has located a SharePoint administrative account and is using it in pursuit of attack progression.
- A user whose learned activity baseline has been lost as a result of a prolonged leave of absence or a change in job function has returned to their regular job
- An admin’s role may have evolved as part of a special project or assignment, requiring SharePoint operations previously outside their normal observed behavior.
Business Impact
- SharePoint is often leveraged across organizations for data which may be sensitive in nature, and desirable to an attacker.
- There exists the potential for the full Office 365 subscription to be compromised if an admin account is taken over.
Steps to Verify
- Investigate both the target and the effect of these operations to understand the full impact.