If you ask security analysts to describe the biggest pain points in their role, you will no doubt get a diverse set of answers. One thing that they will almost certainly have in common is the challenge of dealing with alert fatigue. We’ve observed that challenges in this area come down to three analyst pain points:
- “There aren’t enough hours in the day to deal with the alert volume on my plate.”
- “I am unable to efficiently use my time because I cannot distinguish between the false and true positives.”
- “I’m worried that I will miss a real attack because the signal is buried in the noise of my legacy solution.”
There are many reasons for the pain points described in legacy security solutions, but they largely boil down to:
- Simplistic, condition/anomaly matching creates False Positives.
- An inability to leverage the context clues on the network to improve efficacy.
- A focus solely on detections, and not how to efficiently organize them so that an analyst can focus on the things that actually require their attention.
A better way for Security Analysts:
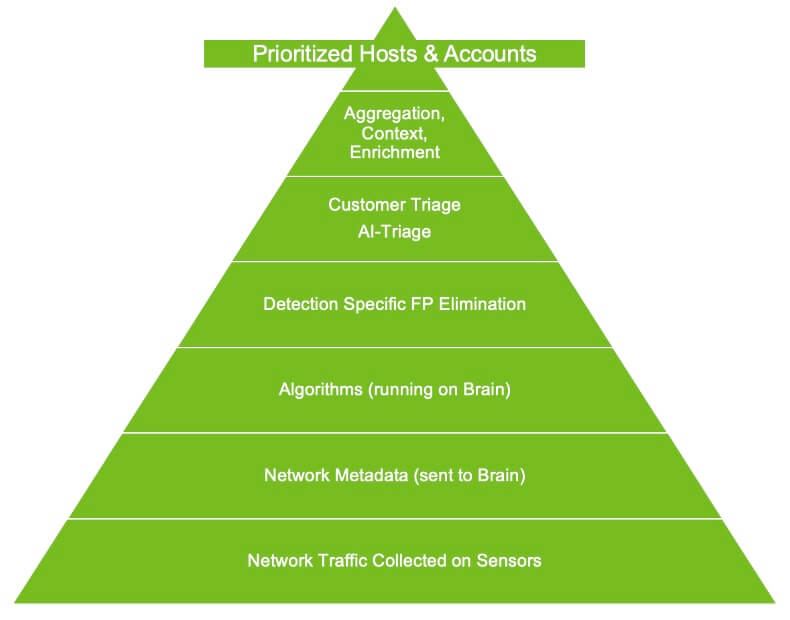
From day one, Vectra has built detections to eliminate the likelihood of false positives by empowering algorithms with context from the network. Where traditional network security products might look simply for a pattern, or statistical anomaly without context, Vectra designs our detections to leverage context from the network and identify anomalies just like a security analyst would.
For instance, our Smash and Grab Exfil detection will learn what data movement is normal on a subnet-by-subnet basis, factor in sites that are popular in your environment, and look for anomalous outbound flows of data, even in encrypted channels. Vectra further correlates the detections across Host and Account entities, learning the archetype and identifying each object, and then prioritizes detections for analysts in an actionable, stack ranked fashion. This dramatically simplifies the effort it takes to operate Vectra compared to competitors who are simply generating detections and leaving it to the analyst to discern the meaning.
But there was still one area we weren’t entirely satisfied with, dealing with True Positives. That's because not all True Positives are malicious. You might also reliably detect activity where the behavior is as the system says it is; in the context in which an event is happening, it may be a benign True Positive rather than a malicious True Positive. For instance, some Anti-Virus products embed file hash lookups within DNS lookups to the AV Vendor. This behavior may look very much like a Command-and-Control channel encoding data within the DNS payload, and that’s because it is. But the fact remains that while this is a true DNS Tunnel, it is not malicious, but rather benign. Our philosophy has been that we will provide visibility into these high-quality detections of attacker behaviors and methods, but balance this by only prioritizing high confidence, correlated, detections at a Host or Account level to the user for attention.
This got us thinking, is there a way that we could apply some of the same techniques that we use to power our world-class ML/AI algorithms to help differentiate between Malicious and Benign True Positives? The goal was to largely eliminate the need for our customers to analyze benign True Positives while prioritizing malicious True Positives for their immediate attention. Thus AI-Triage was born.
Similar to our process for creating our detections, we added AI-Triage capabilities by first analyzing the methodology that real-world analysts apply to resolve these issues. We then trained our ML/AI system to help automate the resolution of the highest confidence scenarios.
How AI-Triage works:
Inherent to the Vectra Platform, AI -Triage works by automatically analyzing all of the active detections in the system, leveraging the context from individual detections, as well as commonalities between detections to look for instances of benign True Positives that we can automatically triage on behalf of the customer. For instance, if we see dozens of endpoints all generating the same hidden HTTPS Tunnel detection to the same destination, over at least 14 days without other indicators of compromise, we can confidently identify this as a benign true positive. AI-Triage will then automatically create a triage rule on the customers' behalf, without requiring any valuable time from the analyst. Should an analyst want to review it, the activity is still available within the platform, but does not require any analyst action, and does not impact the host or account score.
We initially introduced AI-Triage support for C2 and Exfil based detections, and in our upcoming release, we are building on this great framework to extend AI-Triage to Lateral based detections. We’ve observed that AI-Triage reduces overall detections that an analyst would otherwise need to investigate by over 80%, meaning that more time can be spent focusing on events requiring analyst attention.
One-Click Deployment
Now that you know all the benefits AI-Triage offers, you will be pleased to know that you can activate the capabilities with just a single click. AI-Triage requires no tuning or administration whatsoever from the customer. You can enable it, by simply going to Settings -> AI-Triage, and enabling the feature at which point AI-Triage will begin running in the background to identify high confidence benign true positive detections and triaging them for you.
In 30 days since its release, over half of our customers have already turned on AI-Triage. We’re seeing a substantial reduction in benign true positives for the vast majority of customers. But, this is just the beginning of our journey to make security analysts more efficient. We will be extending AI-Triage capabilities to cover new scenarios and other products in our portfolio in upcoming releases.
If you’d like more information on AI-Triage, check out our "AI-Triage in Detail” KB article: https://support.vectra.ai/s/article/KB-VS-1582
For more information about Vectra’s world class ML/AI detection check out: https://support.vectra.ai/s/article/KB-VS-1285







