Triggers
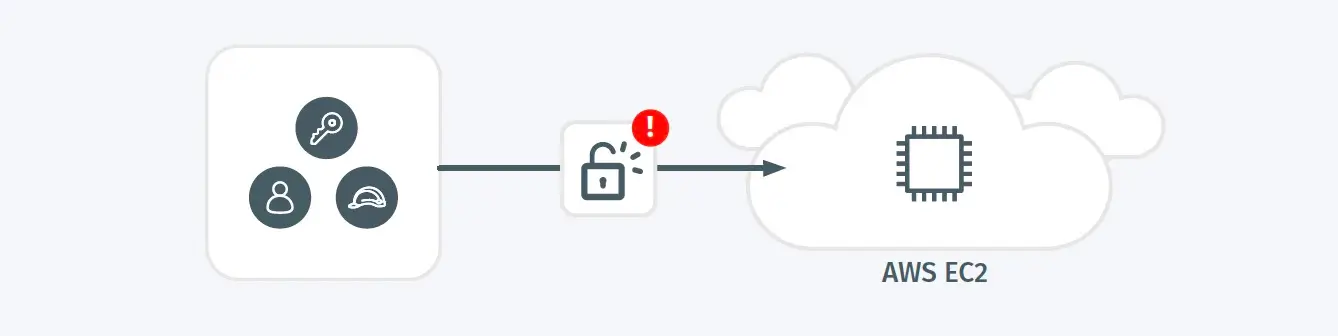
- After enumerating the existing security group policies, the ingress policy for an EC2 instance is modified.
Possible Root Causes
- An attacker is enabling external access to an EC2 instance to maintain persistence.
- An EC2 instance is exposed to external access as a part of its normal operation.
Business Impact
- Once an adversary achieves persistent access, they’ve established the opportunity to stage subsequent phases of an attack.
Steps to Verify
- Validate that any modifications are authorized, given the purpose and policies governing this resource.
- If review indicates possible malicious actions or high-risk configuration, revert configuration and disable credentials associated with this alert then perform a comprehensive investigation.