Triggers
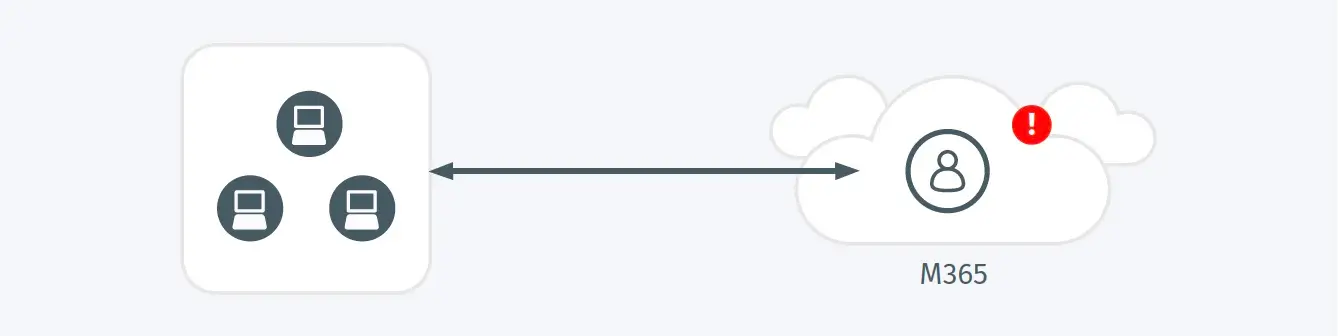
- A new team member has been added to a team in O365 Teams consisting of an external account from a domain rarely associated with O365 Teams access.
Possible Root Causes
- An adversary has added an external account under their control as a new member of a team by abusing an existing O365 Teams account.
- Sometimes legitimate external users (such as partners, contractors, lawyers, auditors, etc.) are added to an O365 Team as part of an authorized activity.
Business Impact
- This type of access enables an attacker to perform additional discovery or collection activities by exposing sensitive business information which may include shared files, meeting content, or chat transcripts.
- The impact of such access may include information necessary to enable further attack progression or facilitate the loss of proprietary information or intellectual property, and regulated data.
- In some cases, access to the team’s communication fabric and conversation history can enable successful blackmail or extortion against enterprise personnel.
Steps to Verify
- Validate that the account added is an authorized member of the O365 Team.