Triggers
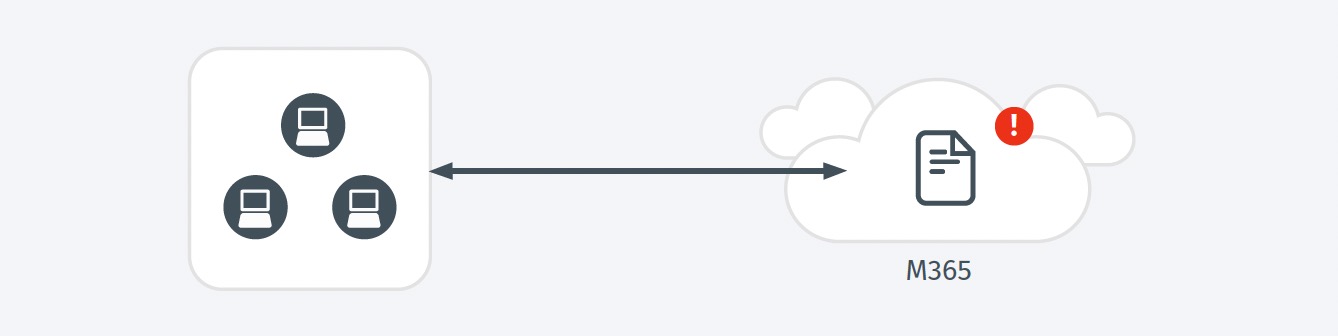
- Files which were subsequently flagged as malware were uploaded into the environment by this account.
Possible Root Causes
- Attackers will stage malicious files in preparation for an attempt to infect other users from a trusted file repository.
- On rare occasions, benign files may be classified as malicious.
Business Impact
- An attacker who has disabled logging may progress parts of an attack without being detected, and without producing an auditable record to aid in forensics.
- Disabling logging degrades a critical component of an organization’s security architecture.
- Many audit and compliance requirements can only be met through the collection of activity logs.
Steps to Verify
- Review whether this logging configuration is expected and appropriate.
- If this is a temporary configuration for troubleshooting purposes, confirm it has been reenabled once that troubleshooting is complete.