Conduct faster, context-driven investigations into active cyberattacks with Vectra and Google SecOps SIEM




Learn all about our partnership.
Download Integration Brief
Modern cyber attackers with sophisticated hacking tools or the right stolen password can easily evade perimeter security to spy and steal inside the network, going largely undetected.
This gap leaves security teams manually chasing down security alerts and events. The inability to determine which alerts pose the highest risk to an organization complicates the task even further.
In practice, this often means breaches are discovered and reported by an external third-party after theft or damage has occurred. This can result in a debilitating post-breach investigation that can cost upwards of millions of dollars, not to mention unwanted negative publicity and brand damage.
The Vectra threat detection and response platform seamlessly integrates AI-based threat hunting and incident response of Google SecOps SIEM Backstory, a global security telemetry platform, for increased context during investigations and hunts and greater operational intelligence.
Together, Vectra and Google SecOps SIEM deliver a practical solution to the most persistent problem facing today’s cybersecurity teams—finding and stopping active cyberattacks.
Key features of integrating Google SecOps SIEM with Vectra AI:
Faster investigations and response
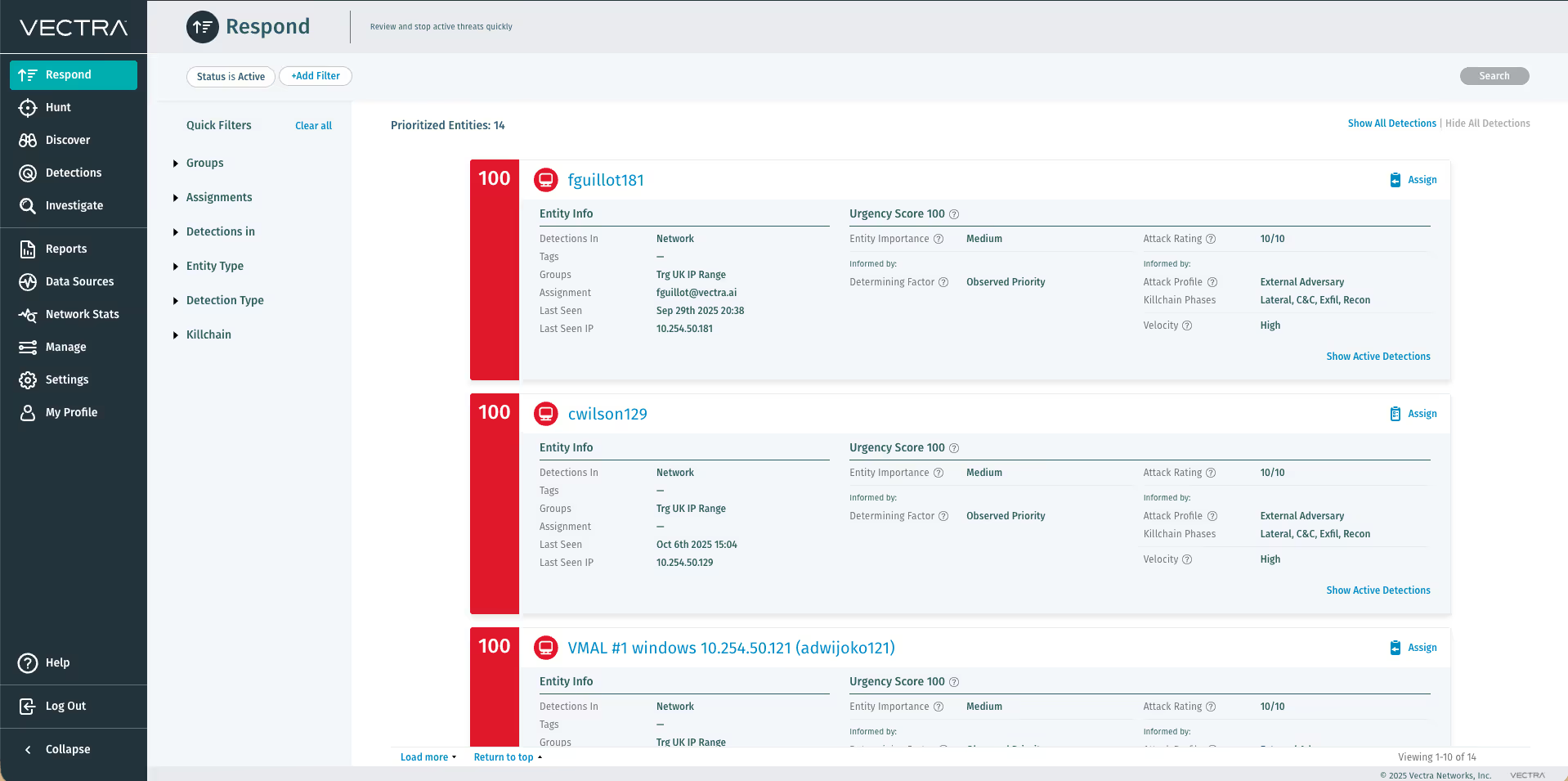
The Cognito platform scores and ranks network hosts by risk. To enable faster investigation and response, all malicious behaviors are automatically associated to the physical network host, even if the IP address changes. Integration of the Cognito and Backstory platforms provides an interactive dashboard to quickly show the number of hosts classified as critical, high, medium and low risk. These scores help security teams prioritize events, eliminating the need to manually triage every event and vastly improving response time.
Full visibility and enhanced threat intelligence
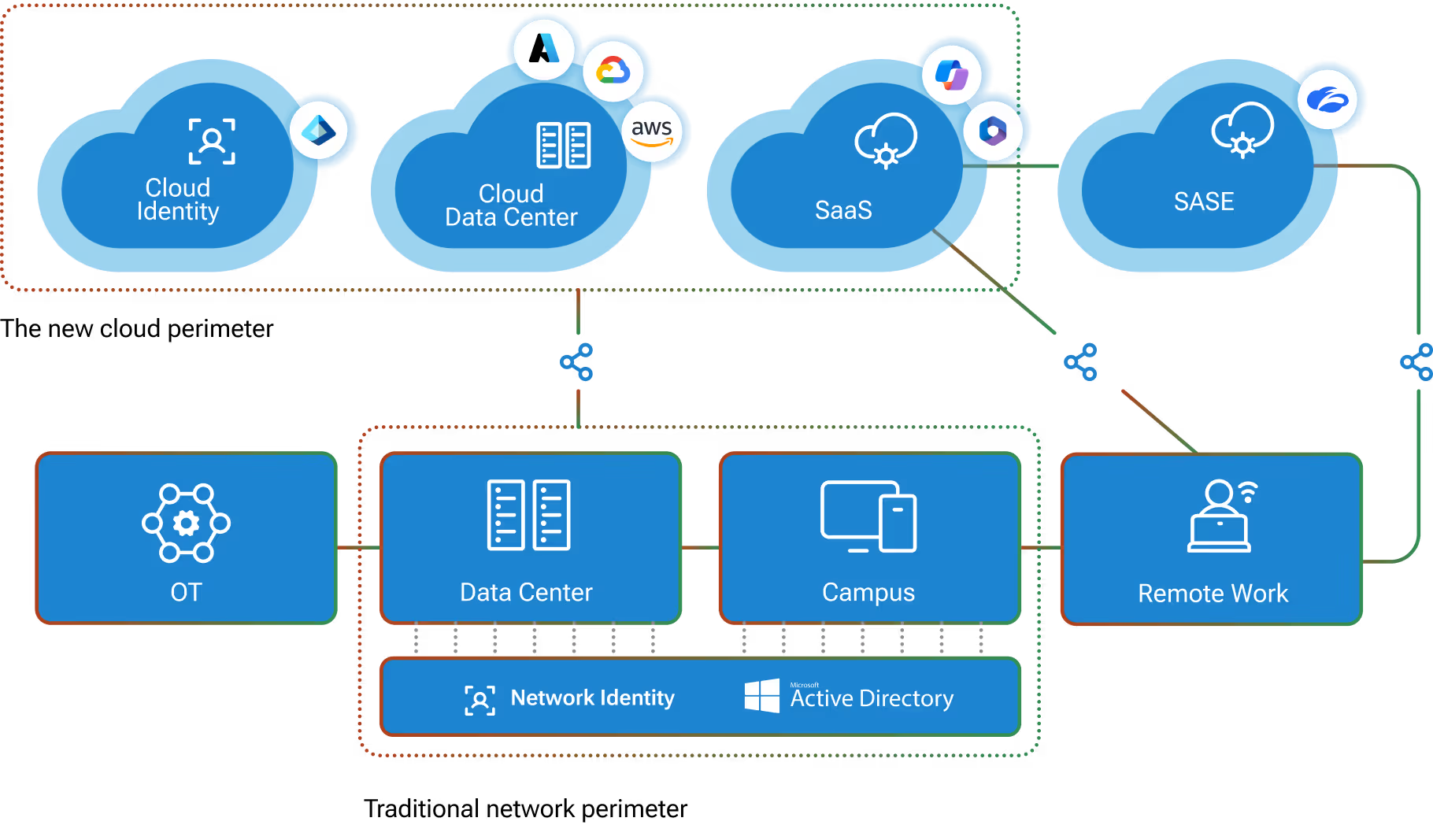
By analyzing all cloud and on-premises enterprise traffic, the Cognito platform reveals threats in all phases of an active cyberattack. Cognito provides this extraordinary range of threat intelligence and security telemetry to the Google SecOps SIEM niche machine-data repository, including detections of unknown malware and attack tools, threats that hide in common applications and encrypted traffic, and in progress threats across every phase of the attack kill chain. This visibility allows security teams to instantly distinguish opportunistic botnet behaviors from more serious targeted threats, enabling quick action before assets are stolen or damaged.
Real-time correlation, additional context and searchable repositories
The Vectra approach to detection enables security teams to detect threats that were missed by other security solutions. The Cognito integration with Google SecOps SIEM Backstory easily connects and correlates Vectra’s findings with other third-party solutions, pulling in additional context for the security team. Google SecOps SIEM also captures, indexes and correlates Cognito threat detections in real time, making them available in a searchable repository so security teams can generate graphs, reports, alerts, dashboards and visualizations.
Key benefits include:
- Quickly mitigate and stop cyberattacks before damage is done
- Gain greater context into every attack by prioritizing infected hosts that pose the highest risk and correlate threats with security telemetry
- Search and analyze threat detections more easily

Google SecOps SIEM and Vectra AI Integration: a superior threat detection model
The Cognito platform uses supervised and unsupervised AI models to detect cyberattacks across all phases of the attack kill chain, ranging from command and control, internal reconnaissance, lateral movement and data exfiltration, without depending on signatures or reputation lists. Cognito detects these threats by analyzing the underlying behavior of attackers from the objective viewpoint of the network. All threat detections are correlated with the hosts involved in the attack, while Cognito’s risk and certainty scores prioritize the hosts posing the highest risk. This enables security teams to detect new and unknown threats, as well as discover attacks that do not rely on malware, such as malicious insiders or compromised user accounts. The integration pulls the Cognito metadata-enriched detections directly into the Google SecOps SIEM Backstory dashboard. Now, organizations can incorporate high-value detections from Cognito into their existing workflows and automate correlation in the Backstory security telemetry, providing greater context to threats and attacks.
The Platform
The Platform
Vectra AI Platform
The integrated signal for extended detection and response (XDR)
Vectra AI Platform
MXDR Services
Technology Integrations