The Cyber Kill Chain: Understanding the 7 Stages of Modern Cyberattacks
Key insights
- Modern AI-powered attacks compress the entire kill chain to minutes, not hours, making automated detection and response essential for organizations operating across hybrid and cloud environments. (Unit 42, Palo Alto Networks 2025)
- The framework has known limitations, including blind spots for insider threats, non-linear attacks, and cloud-native vectors, which is why most mature security teams combine it with MITRE ATT&CK for tactical depth. (MITRE ATT&CK Knowledge Base; Pols, Unified Kill Chain 2017)
The cyber kill chain is a cybersecurity framework that breaks down cyberattacks into sequential stages, from initial target research through data theft or system disruption. Originally adapted from military targeting doctrine by Lockheed Martin in 2011, the framework helps security teams understand how attacks unfold and where to disrupt them.
The model remains widely adopted because it exposes a core attacker dependency: each stage relies on the previous one succeeding. This creates multiple intervention points where a single defensive action can collapse an entire attack operation.
This guide explains how the cyber kill chain works, what each of the seven stages involves, where the framework falls short, and how security teams, SOC analysts, and CISOs can apply it alongside modern approaches like MITRE ATT&CK and behavioral AI detection.
How the cyber kill chain works
The cyber kill chain operates on a straightforward principle: attackers must complete each stage in sequence to reach their objective. This linear progression creates natural chokepoints where defenders can detect, deny, disrupt, or contain adversary operations before damage occurs.
Practitioners often divide kill chain defense into two strategic zones based on where intervention occurs relative to the exploitation phase, the moment when actual compromise happens.
Defense-in-depth aligns naturally with this methodology. Rather than relying on any single control, organizations deploy overlapping defenses targeting different stages:
- Email security disrupts delivery
- Endpoint protection blocks exploitation
- Network monitoring detects command and control
- Data loss prevention catches exfiltration
If one control fails, others can still break the chain. This layered approach is what makes kill chain defense practical, no single tool needs to be perfect.
The 7 stages of the cyber kill chain
The Lockheed Martin cyber kill chain defines seven stages that most cyberattacks follow. Each stage represents a distinct phase of attacker activity and a corresponding opportunity for defenders to intervene. While attackers have grown more sophisticated since 2011, they still cannot skip stages, only compress or disguise them.
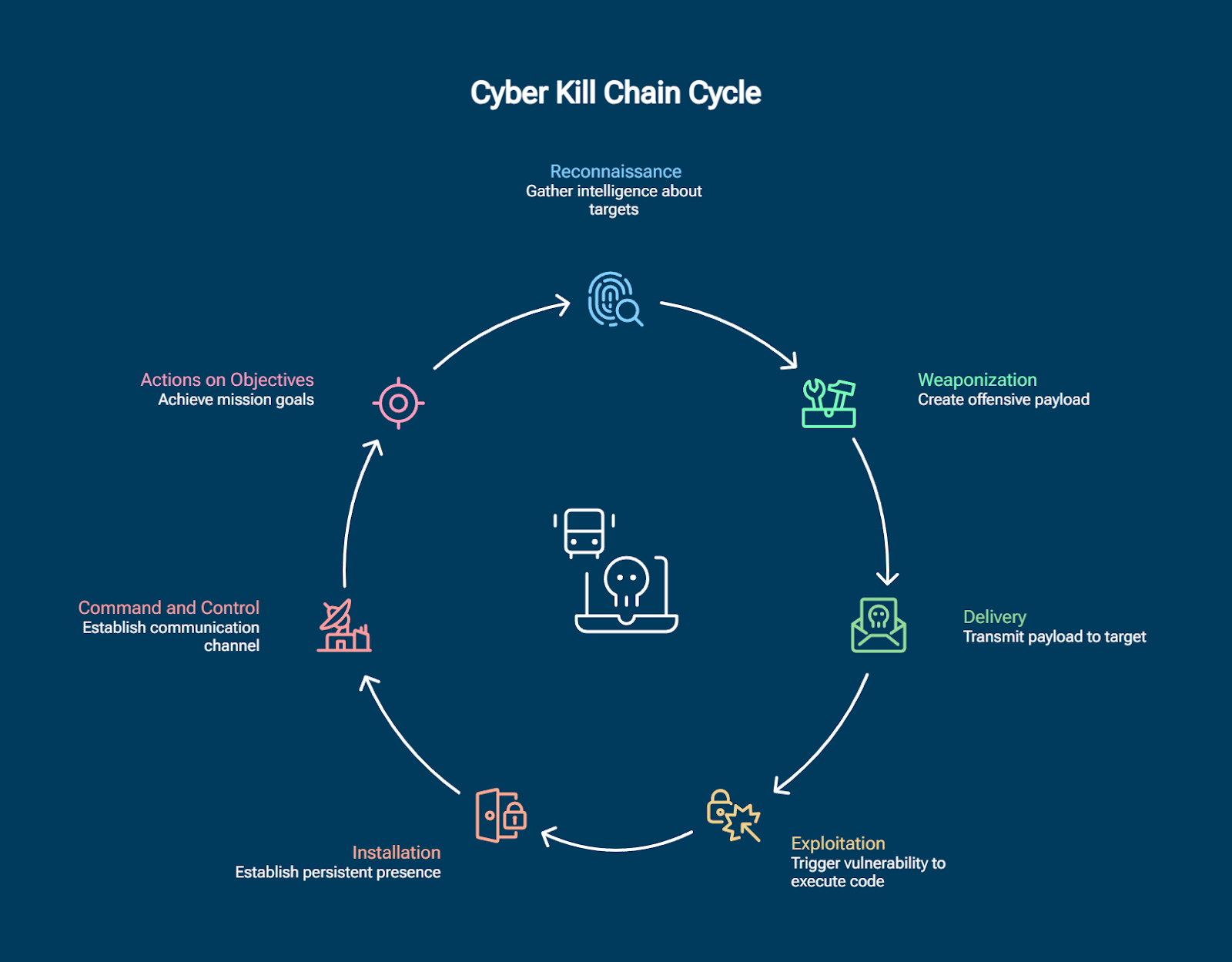
Stage 1: Reconnaissance
Reconnaissance is the opening phase where attackers gather intelligence about potential targets. This includes both passive collection — scanning social media, corporate websites, and public databases — and active probing through network scans and social engineering. Modern reconnaissance leverages automated tools that can profile an entire organization in minutes.
Key defense: Attack surface reduction, digital footprint auditing, operational security (OPSEC) controls, and deception technologies
Stage 2: Weaponization
During weaponization, attackers create or acquire their offensive payload by pairing exploits with remote access tools. This stage occurs entirely within the attacker's environment, making direct detection impossible. Modern weaponization increasingly uses legitimate tools and living-off-the-land techniques, while Ransomware-as-a-Service platforms provide turnkey attack packages.
Key defense: Threat intelligence, exploit trend monitoring, information sharing communities
Stage 3: Delivery
Delivery is the transmission phase where attackers send their weaponized payload to the target. Email remains the dominant vector, but attackers diversify across web downloads, supply chain compromises, cloud service abuse, and USB devices. SEO poisoning, which manipulates search engine results to surface malicious download pages above legitimate ones, has become an increasingly common web-based delivery channel, exploiting trusted user search behavior to bypass email filtering entirely. Phishing and voice phishing attacks continue to rise as social engineering enhances technical delivery. Organizations must assume some delivery attempts will succeed.
Key defense: Email filtering, web proxies, endpoint protection, user awareness training
Stage 4: Exploitation
Exploitation triggers the vulnerability that executes the attacker's code, the moment when theoretical risk becomes actual compromise. Targets include unpatched software, misconfigurations, default credentials, and human psychology. Account takeover through credential phishing or brute force provides authenticated access that bypasses traditional exploit detection entirely, as the attacker simply logs in with valid credentials rather than triggering a vulnerability. Cloud environments introduce additional vectors through API abuse, container escapes, and serverless function manipulation.
Key defense: Patch management, virtual patching, configuration hardening, exploit prevention
Stage 5: Installation
Installation establishes persistent presence in the victim environment, ensuring continued access even if the original entry point is closed. Attackers create backdoors, scheduled tasks, web shells, or abuse cloud service features for persistence. Lateral movement techniques then allow attackers to spread from their foothold.
Key defense: EDR, behavioral analysis, application control, system audits
Stage 6: Command and control
Command and control (C2) establishes the communication channel between compromised systems and attacker infrastructure. Modern C2 uses encrypted channels, domain generation algorithms, DNS tunneling, and legitimate cloud services to evade monitoring. Behavioral analytics and machine learning increasingly supplement traditional monitoring to identify subtle C2 indicators hidden in encrypted or legitimate-looking traffic.
Key defense: Network traffic analysis, DNS monitoring, behavioral analytics, threat intelligence feeds
Stage 7: Actions on objectives
Actions on objectives is the final stage where attackers achieve their mission: data theft, ransomware deployment, system destruction, or establishing long-term access for espionage. Once attackers reach this stage, damage is often significant, which is why breaking the chain at earlier stages is far more effective and less costly.
Key defense: Data loss prevention, immutable backups, network segmentation, incident response plans
Is there an eighth stage in the cyber kill chain?
Many security practitioners now include monetization as an eighth stage, reflecting cybercrime's evolution into a profit-driven industry. Attackers convert access into revenue through ransomware payments, stolen data sales on dark web markets, cryptocurrency theft, or selling network access to other criminal groups through initial access brokers. The rise of Ransomware-as-a-Service platforms, where developers, affiliates, negotiators, and money launderers each specialize in different functions, exemplifies how monetization has become a structured criminal supply chain.
Real-world cyber kill chain examples
Mapping real-world incidents to kill chain stages reveals how the framework translates from theory to practice. Modern attacks increasingly compress the timeline, cloud-based incidents can complete full kill chain progression in minutes rather than hours, leaving defenders virtually no time for manual response.
The Qilin ransomware group exemplifies how modern security hackers compress the kill chain. Rather than conducting their own reconnaissance and delivery, Qilin operators purchase network access from initial access brokers, skipping the earliest stages entirely. Once inside, they use legitimate tools like PowerShell and WMI for internal reconnaissance, systematically destroy backups, then deploy ransomware, often completing the entire sequence within hours.
These examples highlight a consistent pattern: attackers deliberately exploit gaps between security tools, targeting the spaces where endpoint detection, identity monitoring, and network visibility fail to overlap.
What are the limitations of the cyber kill chain?
The cyber kill chain has significant limitations that security teams should understand before relying on it as their sole defensive framework. Recognizing these gaps helps organizations determine where complementary approaches are needed.
- Linear assumption: The sequential model doesn't account for attacks that skip, repeat, or execute stages simultaneously. Cloud-native and supply chain attacks often bypass early stages entirely.
- Perimeter and malware focus: The original framework was designed for malware-driven intrusions. It does not adequately address identity-based attacks where adversaries authenticate with stolen credentials and move laterally without deploying payloads.
- Insider threat blind spot: Trusted users with legitimate access bypass reconnaissance, weaponization, and delivery entirely, making most of the kill chain irrelevant for insider threat detection.
- Cloud-native gaps: Ephemeral infrastructure, API-based attack vectors, and shared responsibility models introduce attack paths the original framework was not designed to cover.
Despite these limitations, the kill chain remains valuable as a strategic communication tool and a starting point for defense planning. Most mature organizations address its gaps by combining it with MITRE ATT&CK for tactical depth and behavioral detection for identity and network-layer visibility.
Cyber kill chain vs MITRE ATT&CK
The cyber kill chain and MITRE ATT&CK are complementary frameworks that serve different purposes. The kill chain provides a high-level strategic view of attack progression through seven sequential stages, making it useful for executive communication and resource allocation. MITRE ATT&CK offers granular tactical detail with 14 tactics and over 200 techniques based on observed real-world attacker behavior, without assuming linear progression.
The granularity difference becomes clear when mapping a single kill chain stage to its ATT&CK equivalent:
Where the kill chain identifies that reconnaissance is occurring, MITRE ATT&CK specifies the exact technique, enabling precise detection engineering and measurable coverage tracking.
The Unified Kill Chain, introduced in 2017 by Paul Pols, attempts to merge both frameworks' strengths across 18 stages with non-linear progression paths. Most practitioners recommend starting with the original seven-stage model for strategic alignment, then layering MITRE ATT&CK for tactical implementation.
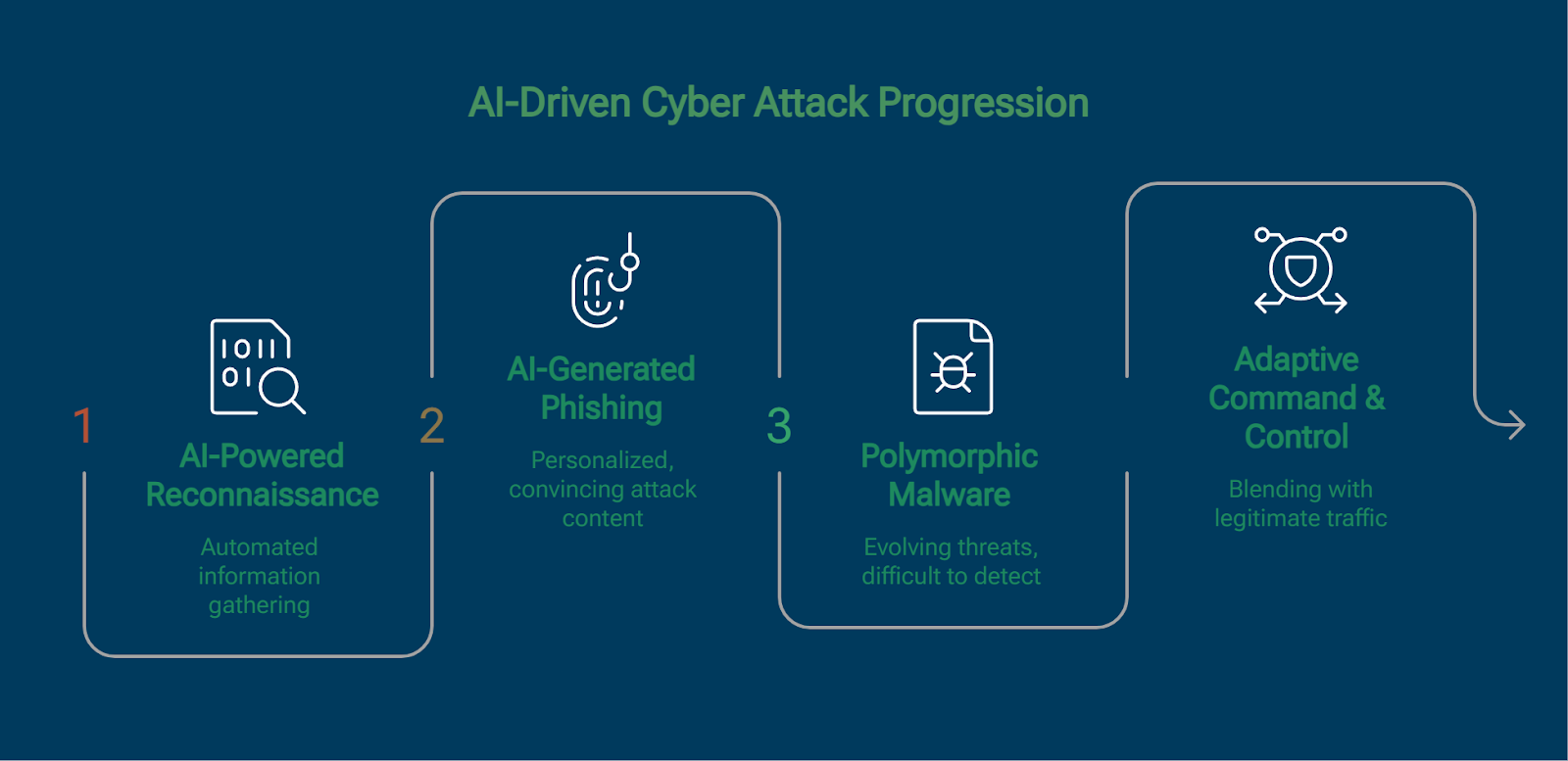
The AI kill chain: how AI changes attack progression
Artificial intelligence has compressed the cyber kill chain from weeks to minutes. Attackers use AI for automated reconnaissance, AI-generated phishing content, polymorphic malware creation, and adaptive command and control communications that blend with legitimate traffic. The result is a dramatically shorter attack timeline where each stage executes faster than human-driven defense can respond.
Defensive AI creates equally significant improvements:
- Machine learning detects reconnaissance by identifying deviations from behavioral baselines
- Natural language processing flags weaponized documents before delivery
- Behavioral analytics identify exploitation and lateral movement that signature-based tools miss
- Cross-stage signal correlation surfaces attack progression invisible when stages are analyzed in isolation
As AI-driven attacks become the norm, organizations that rely solely on manual triage and rule-based detection face an inherent speed disadvantage. Automated detection and response across all kill chain stages is becoming a baseline requirement, not a differentiator.
Detecting and preventing kill chain progression
Effective kill chain defense requires detection capabilities mapped to every stage, automated response actions, and continuous threat hunting. The shift from reactive to proactive operations is why network detection and response, managed detection and response services, and extended detection and response platforms have become central to modern security architectures.
The following table maps each kill chain stage to the specific attacker actions defenders should expect and the countermeasures designed to disrupt them.
Behavior-based detection has emerged as essential for identifying attacks that evade signature-based tools. By baselining normal activity and correlating deviations across multiple stages, a user accessing unusual file shares, connecting to rare external IPs, and transferring large data volumes, behavioral platforms reveal kill chain progression invisible to individual security tools.
Breaking the chain demands both tactical disruption (technical controls at each stage) and strategic disruption (increasing attacker costs through deception, threat intelligence sharing, and coordinated response). Early-stage disruption is significantly less costly than post-compromise remediation.
Behavioral detection across the cyber kill chain
The Vectra AI Platform detects attacker behavior across kill chain stages by analyzing network, identity, and cloud activity, rather than searching for known indicators of compromise. This behavioral focus recognizes that while specific tools and techniques constantly change, the underlying actions attackers must take at each stage remain consistent.
Hybrid AI combining supervised and unsupervised machine learning provides coverage across the full kill chain. Supervised models detect known patterns with high accuracy. Unsupervised models surface novel attacks by identifying anomalous behaviors that no signature could anticipate. Correlation across SIEM alerts, endpoint detections, and network signals exposes complete attack progressions that individual tools miss.
Sources and methodology
This guide draws on established cybersecurity frameworks, published threat intelligence, and documented real-world incidents. The following sources inform the definitions, statistics, and defensive recommendations throughout the page.
- Frameworks: Lockheed Martin Intelligence Driven Defense® and Cyber Kill Chain® (2011), MITRE ATT&CK knowledge base, MITRE D3FEND countermeasures, Unified Kill Chain model by Paul Pols (2017)
- Threat intelligence: Unit 42 (Palo Alto Networks) incident response and threat research, published vendor threat intelligence reports (2024–2025)
- Attack examples: Publicly documented ransomware group operations (including Qilin) and cloud security incidents reported during 2024–2025
Defensive alignment: NIST Cybersecurity Framework functions (Identify, Protect, Detect, Respond, Recover)
FAQs
In which stage of the cyber kill chain is malware developed?
Malware is developed during the weaponization stage (stage 2). In this phase, attackers create or customize offensive payloads by combining exploits with remote access tools, backdoors, or ransomware. Because weaponization happens entirely within the attacker's own environment, defenders cannot directly observe it. Threat intelligence, tracking emerging malware families, exploit kits, and adversary tooling, is the primary way organizations prepare for weaponized payloads before they arrive.
Can the cyber kill chain detect insider threats?
The traditional cyber kill chain has significant limitations for insider threat detection because malicious insiders bypass early stages entirely, they already have access and do not need reconnaissance, weaponization, or delivery. However, insider threats still generate detectable signals during later stages: unusual data access patterns (actions on objectives), privilege escalation attempts (installation), and abnormal data transfers (exfiltration). Organizations address this gap by combining the kill chain with user and entity behavior analytics and zero-trust architectures.
How many stages are in the cyber kill chain?
The original Lockheed Martin framework defines seven stages: reconnaissance, weaponization, delivery, exploitation, installation, command and control, and actions on objectives. Many practitioners now include an eighth stage, monetization, to reflect how modern attackers convert access into revenue through ransomware, data sales, or access brokering. The Unified Kill Chain extends the model further to 18 stages for more granular coverage of modern attack patterns.
What is the Unified Kill Chain?
The Unified Kill Chain, introduced in 2017 by Paul Pols, extends the original framework to 18 stages organized into three phases: Initial Foothold, Network Propagation, and Action on Objectives. It addresses key limitations of the original model by incorporating non-linear attack paths, lateral movement, privilege escalation, and defense evasion as explicit stages. While more comprehensive, its complexity is best suited for mature security teams. Most practitioners start with the seven-stage model and expand as organizational security maturity increases.
How long does a typical kill chain attack take?
Attack timelines have compressed dramatically. Cloud-based attacks can achieve full kill chain progression in under 10 minutes. Ransomware operators using initial access brokers often move from first access to encryption within hours. Nation-state actors conducting espionage may spend months in reconnaissance before acting. The variance depends on attacker sophistication, target environment, and objectives, but the trend across all attack types is faster progression, which makes automated detection and response increasingly essential.
Which industries use the cyber kill chain?
Every major industry applies the cyber kill chain, though implementation varies by threat landscape. Financial services focus heavily on the delivery and actions on objectives stages where monetary theft occurs. Healthcare adapts the framework for medical device security and ransomware resilience. Critical infrastructure sectors must account for cyber-physical impacts at the actions on objectives stage. Government and defense organizations pioneered kill chain adoption and continue to advance the framework.
Is the cyber kill chain still relevant in 2026?
The cyber kill chain remains highly relevant when used as part of a multi-framework defense strategy. Its core insight, that attacks are sequential and can be disrupted at any stage, is unchanged. Limitations around insider threats, non-linear attacks, and cloud-native vectors are well documented and addressed by complementary frameworks like MITRE ATT&CK. Leading security platforms, industry certifications, and regulatory frameworks all reference kill chain concepts. The framework is most effective as a strategic planning and communication tool, supplemented by MITRE ATT&CK for tactical operations.