The recent Iran–Israel escalation has sparked a spike in cyber operations from state-linked actors zeroing in on identity, cloud, and enterprise networks. These well-resourced groups combine deep network intrusions with identity abuse to slip past traditional defenses.
They exploit public-facing apps for initial access, harvest credentials via phishing or password spraying, then move laterally with RDP, PsExec, or remote-access services. Persistence comes through scheduled tasks, DLL sideloading, hidden windows, and protocol tunneling. Data is quietly staged, archived, and exfiltrated over obscure channels often without triggering legacy alerts.
Simultaneously, they launch identity-focused campaigns inside Microsoft 365, Azure, and Google Workspace: abusing OAuth, bypassing MFA, and weaponizing Outlook, OneDrive, and Teams to maintain access and siphon data. These tactics target critical infrastructure, government, commercial enterprises, and NGOs across the Middle East and the West—blending espionage and destructive attacks (wipers, forced encryption).
Relying only on endpoints or perimeter controls leaves you blind to the full attack chain. If you use cloud collaboration, hybrid infrastructure, or remote access, you’re already in their sights.
Recent Activity from Iranian Threat Actors
Iranian threat groups continue to run sustained cyber operations against organizations across government, telecommunications, energy, and technology sectors. Recent campaigns show actors like MuddyWater expanding their use of identity abuse and cloud-native tooling while maintaining traditional PowerShell-based intrusion techniques. Rather than deploying obvious malware, these operators increasingly rely on scripts, legitimate administration tools, and compromised infrastructure to maintain stealth across hybrid environments.
Who’s Behind the Attacks: Iran-Linked APT Profiles
Despite varying goals (ranging from long-term espionage to outright sabotage) each group leverages both network and identity channels to breach, persist, and extract. Below is a high-level view of their initial access, network TTPs, and identity/cloud TTPs.
Iranian threat groups frequently reuse tooling across campaigns, particularly PowerShell frameworks, script loaders, and open-source remote access tools. This reuse makes behavioral detection across identity and network telemetry especially effective.
Five Identity and Cloud Techniques SOC Teams Must Monitor
Iran-affiliated threat actors are moving beyond traditional malware and exploits. Their campaigns now hinge on abusing identity systems and living within the trusted tools your organization already uses. These five techniques are central to how they evade detection and maintain persistence in cloud environments. Each represents a critical visibility gap if your team is relying on traditional EDR or SIEM tools alone.
- Credential Theft via Spear Phishing
Fake login portals mimicking Office 365 or Gmail, password spraying, and MFA-bypass techniques. - Cloud Account Hijacks
Using stolen credentials to access email, OneDrive, SharePoint, or Azure apps. - Recon and Lateral Movement
Enumerating Entra ID (Azure AD), creating rogue OAuth apps or subscriptions for persistence. - Data Exfiltration via Legitimate Tools
Moving data through OneDrive, Outlook, or web-based APIs to hide within normal traffic. - Living-Off-the-Land Scripts and Cloud Tools
Iranian threat actors increasingly rely on PowerShell loaders, administrative scripts, and legitimate cloud APIs instead of custom malware.
Why Iranian APTs Are Targeting Cloud and Identity
For Iranian threat groups, cloud platforms and identity systems offer scale, stealth, and strategic access. These attackers are adapting their operations to match how organizations actually work today. Remote access, federated identity, and cloud-first infrastructure have created a wide attack surface where traditional controls often lack visibility.
Key reasons these environments are attractive targets include:
- Identity is the new perimeter. Once attackers obtain valid credentials tied to SaaS platforms or cloud admin roles, they often bypass traditional defenses entirely. Security tools focused on endpoints or firewalls rarely flag authenticated API calls or abnormal login behavior when the session appears legitimate.
- Cloud environments provide operational cover. Iranian APT groups frequently operate within sanctioned applications such as Microsoft 365, Azure, and Google Workspace. They exploit weak OAuth policies, misconfigured conditional access rules, and excessive privileges to maintain persistence while blending into normal user activity.
- Hybrid networks create pivot opportunities. Many organizations maintain links between on-prem systems and cloud environments. Iranian actors have abused identity synchronization services and hybrid management tools to pivot from compromised internal systems into cloud tenants, allowing them to expand access across environments.
- Living-off-the-land scripting reduces malware visibility. Recent campaigns from groups such as MuddyWater show heavy reliance on PowerShell loaders and script-based frameworks that execute payloads directly in memory. Instead of deploying obvious malware, attackers retrieve tools dynamically and operate using native system capabilities.
- Cloud-native tooling is dual-use.Tools like Microsoft Graph API, PowerShell, Outlook, Teams messaging, and remote administration software are designed to enable productivity. Iranian actors routinely use these same capabilities to enumerate environments, move laterally, and exfiltrate data while remaining difficult to distinguish from legitimate activity.
In short, cloud and identity attacks allow Iranian APT groups to operate quietly across hybrid environments. They blend into legitimate user behavior, avoid traditional defenses, and exploit visibility gaps that many organizations still struggle to monitor effectively.
Security Controls to Disrupt Iranian APT Tradecraft
To reduce your exposure to the techniques detailed above and make your environment a harder target, we recommend the following immediate actions:
- Enforce Multi-Factor Authentication to stop phishing and MFA bypass.
- Enable Conditional Access and device policies on cloud/SaaS accounts.
- Monitor login activity for suspicious IPs, unusual geographies, and VPN-originated logins.
- Lock down OAuth apps and permissions: review all app consents and service accounts in Microsoft 365/Azure.
- Audit privileged accounts regularly especially those with admin roles within Exchange/Azure.
- Implement User Training: recognize fake login portals and social engineering tactics.
- Monitor for data exfiltration: set up DLP rules and Cloud Access Security Broker (CASB) policies.
- Check MFA push behaviour: restrict notifications after repeated failed attempts or use phishing-resistant MFA options like FIDO2.
These controls harden your environment but detecting credential misuse and network stealth requires active, behavior-driven visibility.
Turn Iranian APT Intelligence Into Immediate Threat Hunting
Understanding how Iranian threat groups operate is only the first step. The next challenge is determining whether those same techniques are already happening inside your environment.
SOC teams don’t need another report explaining attacker tradecraft. What they need are concrete ways to test their environment for those behaviors.
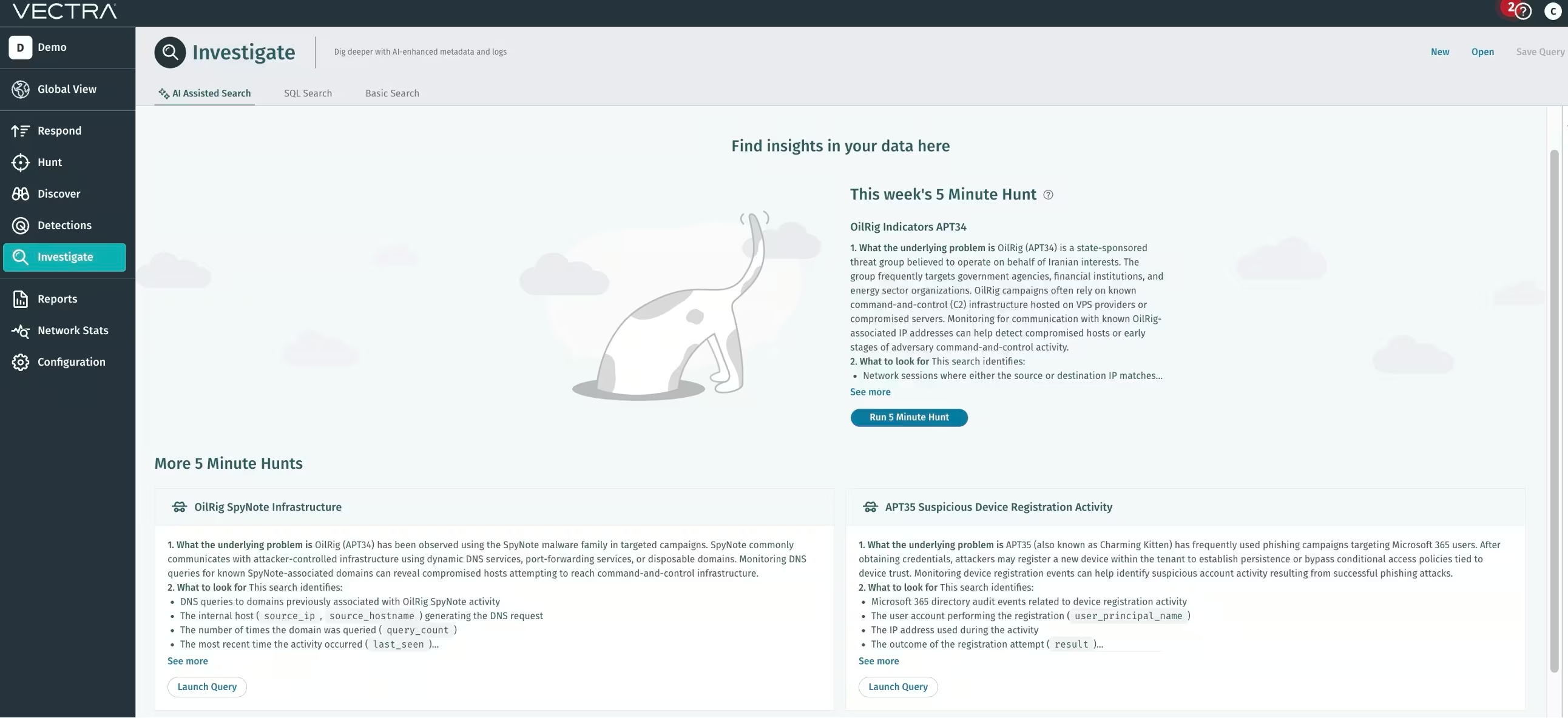
To help security teams move from intelligence to investigation, we created a set of threat hunts tied directly to Iranian APT tradecraft observed in recent campaigns. These hunts surface early indicators across identity and network activity, including:
- Suspicious Microsoft 365 device registrations linked to credential compromise
- OilRig command-and-control infrastructure communication
- SpyNote and QasarRAT DNS activity tied to attacker infrastructure
- Failed device registrations that may indicate APT35 reconnaissance
- Network sessions associated with Pupy malware infrastructure
Each hunt includes a ready-to-run query you can execute inside the Vectra AI Platform to quickly identify potential attacker activity.
Running targeted hunts like these helps analysts move from passive monitoring to proactive detection. Instead of waiting for alerts, your team can directly search for the behaviors Iranian operators rely on once they gain access.
Because these actors blend identity abuse, SaaS activity, and network infrastructure, effective detection requires visibility across all three.
That’s exactly where the Vectra AI Platform provides an advantage.
How the Vectra AI Platform Exposes Iranian APT Activity
Traditional security tools tend to focus on isolated signals: endpoint alerts, firewall logs, or authentication events. Iranian threat actors operate across identity systems, SaaS platforms, and network infrastructure simultaneously, which makes those siloed approaches easy to evade.
The Vectra AI Platform continuously analyzes behavior across: Network traffic Active Directory and Entra ID Microsoft 365 identity activity Cloud platforms including AWS and Azure Instead of relying on static indicators, the platform identifies abnormal behavior that signals compromise even when attackers use legitimate credentials or sanctioned cloud tools.
This gives SOC teams the visibility needed to detect the exact techniques used by Iranian APT groups: credential abuse, identity manipulation, stealthy lateral movement, and covert command-and-control activity.
According to IDC, organizations using Vectra AI identify 52% more threats in at least 50% less time.
Here’s how Vectra AI detects each of the five core techniques used by Iranian APTs:
The Vectra AI Platform does not require agents. It integrates natively with Microsoft and applies real-time detection logic tailored to identity-driven attacks. This approach delivers precise, high-fidelity alerts and automated response capabilities that empower SOC teams to act decisively without drowning in false positives.
Already a Vectra AI NDR customer?
To defend against this new wave of identity and cloud-centric attacks, we strongly recommend expanding your existing deployment with Identity and Cloud coverage. This ensures unified visibility and protection across hybrid environments where these threat actors thrive.


