Threats are stealthy and can stay hidden over long periods of time while they exfiltrate data within allowed traffic channels. With increasingly sophisticated threats, security teams need accurate and continuous monitoring for threat activity across all environments.
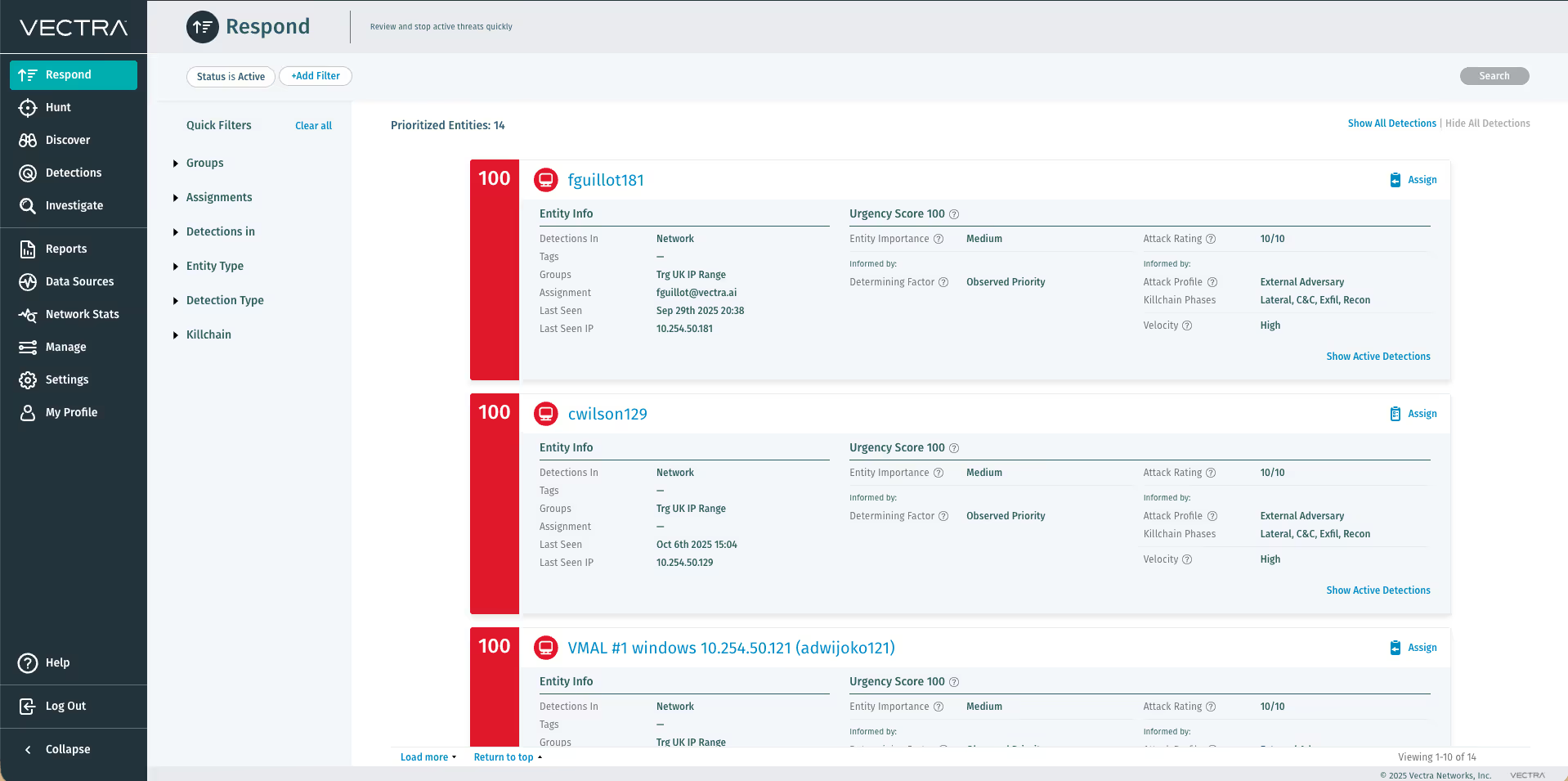
The success or failure of a security team often boils down to time-to-response. Once identified, threats must be contained immediately and malicious activity blocked.
Even after the detection, response may require hours or days of investigation from highly trained security analysts to stop the damage and return to normal operations.
The integration between the Vectra automated network detection and response platform and Check Point Next Generation Firewalls empowers security staff to quickly expose hidden attacker behaviors, pinpoint specific hosts involved in a cyberattack and contain threats before data is lost.
Timely response to threats starts with Check Point SandBlast Zero-day Protection. Check Point SandBlast Zero-Day Protection is a cloud-based sandboxing technology where files are quickly quarantined and inspected, running in a virtual sandbox to discover malicious behavior before they enter the network. SandBlast detects malware at the exploit phase, even before attackers can apply evasion techniques attempting to bypass the sandbox.
Key integration benefits include:
Empower analysts to stop attacks
Finding and retaining qualified security staff is a challenge for most organizations. Even in the best of cases, most networks generate more security alerts than staff have the time to analyze. The powerful combination of Vectra threat detection and response with Check Point Next Generation Firewall prevent-first enforcement makes the best use of time and talent. Security teams can quickly pinpoint the hosts involved in an active cyberattack, verify the threat with on-demand forensics and trigger a dynamic containment of the affected devices—all from within the intuitive Vectra user interface. Automation empowers staff to find and resolve issues quickly, saving time and money.
Automate containment based on risk and certainty
Many behavioral analysis solutions simply flag anomalies, which then require extensive analysis and follow-up to determine an appropriate response. This leads to a bottleneck from human analysis and security staff who suffer from alert fatigue. Ultimately, delayed responses and missed alerts can result in attackers successfully exfiltrating company data. In addition to automating the hunt for threats, the Vectra platform automatically scores each detection and affected host in terms of risk to the network and the certainty of the attack. These scores retain context over time and correlate the progression of an attack, allowing staff to prioritize the most urgent issues first. Security staff can use Vectra threat-level and certainty scores to drive dynamic blocking rules aligning to the risk profile of the organization.
Key benefits include:
- Prevent zero-day threats by deploying security that detects and prevents threats first
- Automate threat response by combining behavior-based threat detection with real-time enforcement
- Empower security analysts to respond to threats using simple event tags
- Take focused blocking actions, such as blocking based on type of threat, risk and certainty.
Intelligent threat detection
Enterprises can augment Check Point prevent-first security with Vectra. The Vectra platform accelerates customer threat detection and investigation using sophisticated artificial intelligence to collect, store and enrich network metadata with insightful context to detect, hunt and investigate known and unknown threats in real time. Vectra integrates seamlessly with Check Point Next Generation Firewalls, dynamically blocking malicious traffic. Blocking can be fully automated based on the type of threat, as well as threat and certainty scores of specific hosts, such as hosts subject to Payment Card Industry (PCI) regulations. With Check Point prevent-first Next Generation Firewalls augmented with Vectra automated threat detection and response, security teams can condense weeks of work into seconds and take action before damage is done.