With around 65,000 ransomware attacks expected this year in the US alone according to Yahoo! Finance, let’s just go out on limb here and say that folks are having a rough go at stopping these menacing occurrences. It doesn’t seem to matter which region, country or industry you’re in, cybercriminals have proven that they will launch ransomware attacks on any organization that they can extort money from or steal something of value. So, does this mean that it’s only a matter of time before you find yourself in a pickle between paying a hefty ransom or saying goodbye to critical assets and data?
That sounds like a pickle that will make your face pucker, and if you listen to what Vectra CEO, Hitesh Sheth has been saying all along—solving for ransomware requires a new way of thinking. These attacks can’t be prevented with many of the current security strategies that organizations have in place. However, it is possible to detect when something out of the ordinary happens in your environment in away that will allow your security team to contain malicious events like ransomware attacks. In fact, if we take a look at the industry insights pulled from the Vectra Spotlight Report, Vision and Visibility: Top 10 Threat Detections for Microsoft Azure AD and Office 365, you’ll have a good understanding about how detections can keep your team informed about the behaviors inside your environment.
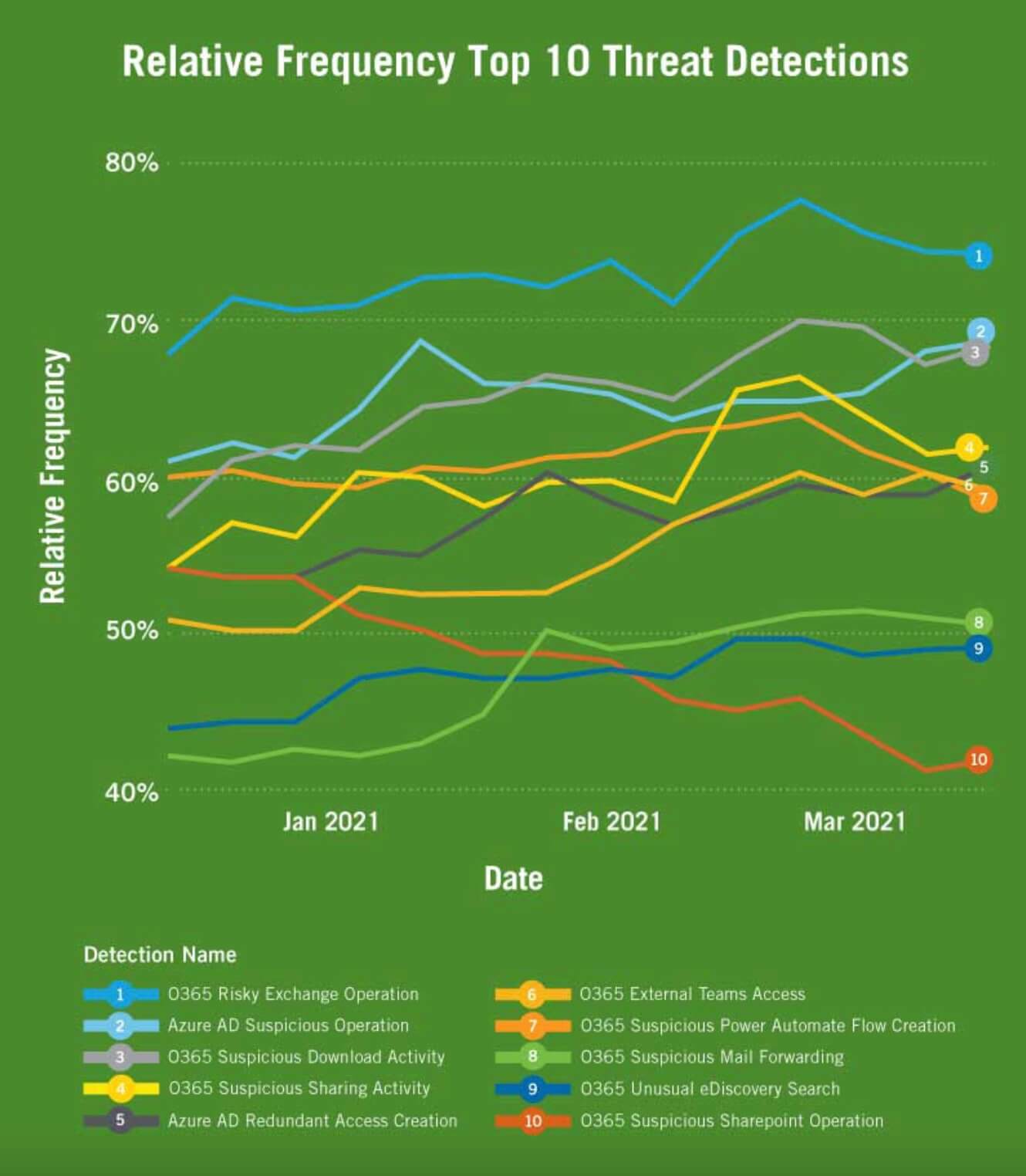
We’ve taken the report as step further and broken down the insights by industry to provide both a view of the cloud security concerns for certain industries as well as how detections would map back to attacker behavior like in ransomware or supply chain attacks. All of this starts with being able to collect the right data and having threat-driven artificial intelligence (AI) that will allow you to pinpoint the ins and outs of attacks and focus on threats that need to be stopped. The industry insights below are all based on real-life, anonymized customer data—these are the detections customers receive to ratify attacks across Office 365 and Azure AD. Let’s get into some of the highlights:
Healthcare
As we witnessed with the attack on Ireland’s Health Service Executive (HSE), ransomware attacks on healthcare organizations can mean stolen medical records and data, but also go way beyond being just a technology issue in that they have the potential to diminish the quality of life and care that people need to survive.
The most frequent detection seen across the Vectra healthcare customer base was O365 Suspicious Power Automate Flow Creation, which could indicate that an attacker is configuring a persistence mechanism. Microsoft Power Automate is no doubt a helpful tool for automating mundane tasks, but the risk is that it’s on by default in Office 365 and comes standard with hundreds of connectors. It’s appealing to attackers because even with basic, unprivileged access it can be used as a channel for them to live off the land and work towards their goals. Read more healthcare industry insights to see how Vectra healthcare customers are ratifying attacks in their environments.
Manufacturing
As an industry that prioritizes operational uptime, ransomware has the ability to halt operations in a hurry which makes manufacturing organizations a prime target for cyberattacks. A ransomware attack that impacts operations would put pressure on a facility to react by paying the ransom in order to limit any equipment shutdowns. While many manufacturers deploy a physically distributed network, they’re also adopting cloud for speed, scale and connectivity like other industries which adds another layer on top of the attack surface.
In taking a look at the frequent detections Vectra manufacturing customers receive, two of the top three were related to Office 365 sharing activity. Any suspicious sharing activity should be scrutinized by security teams to make sure that the actions are being made by authorized users and not that of an attacker attempting to exfiltrate data or anything that would help criminals move further into an attack progression. To read more about the suspicious activity these organizations should have on their radar, see the full industry insights on manufacturing.
Financial Services
If there’s a more appealing target for cybercriminals than Financial Services Institutions (FSI), we’d love to hear about it. This is one of the reasons the industry remains one of the most heavily regulated, and now with cloud adoption soaring, cybercriminals just have more angles to try to leverage for attacks. Specifically in Office 365 and Azure AD, Vectra FSI customers cited a high percentage of O365 Risky Exchange Operation and Azure AD Redundant Access Creation. Whether there’s a possibility of an attacker manipulating Exchange to gain access or attempting an account takeover, this activity is concerning and should be investigated by security teams when spotted. Get more details about what these detections mean by reading the full industry insights on FSI.
Education
The pandemic left education institutions scrambling for solutions to keep students and educators safe, connected and productive which in many cases meant—reaching for the cloud. Whether it was communication or productivity tools, the cloud proved to be up to the task and in many ways made it possible for learning through this time to be a reality. But as was the case with the other industries above, the cloud changed what was known about security for education institutions as well. We saw email and sharing activity trigger threat detections in higher education institutions, which was no surprise as this enables learning and collaboration but it also makes it more difficult to spot malicious data leakage. To see which detections education (EDU) customers are using to ratify attacks, take a look the EDU industry insights.
Time to start understanding your account behavior
If you take a look at any of the industry insights mentioned here or the full spotlight report, you’ll see why it’s critical for organizations to deploy a clear vision of what authorized use looks like along with the visibility to monitor and measure deviations from that vision. Without these two things, threat detection becomes a difficult challenge because you won’t know whether the activity you’re seeing is from an authorized user or motions by an attacker. And when you think about how improbable it is to prevent a ransomware attack with traditional endpoint security tools that cybercriminals regularly bypass, here’s never been a better time to truly know your account behavior.
Check out the Spotlight Report, now!


