The Maze ransomware, previously known in the community as “ChaCha ransomware,” was discovered on May 29, 2019 by Jerome Segura. Although over a year old at this point, it is still seen in the wild as the recent attack on Canon shows. Like other ransomware, Maze spreads across a corporate network, infecting computers it finds and encrypts data so it cannot be accessed.
How does Maze Ransomware works?
In addition to encrypting data, Maze also steals the data it finds and exfiltrates it to servers controlled by the attacker who then threaten to release it if a ransom is not paid. Increasingly, other ransomware (such as REvil, also known as Sodinokibi) have been observed using similar tactics.
Maze and similar ransomware attacks leverage encrypted command and control (C2), deception, and the use of native Windows functions to avoid detection by signature-based security controls.
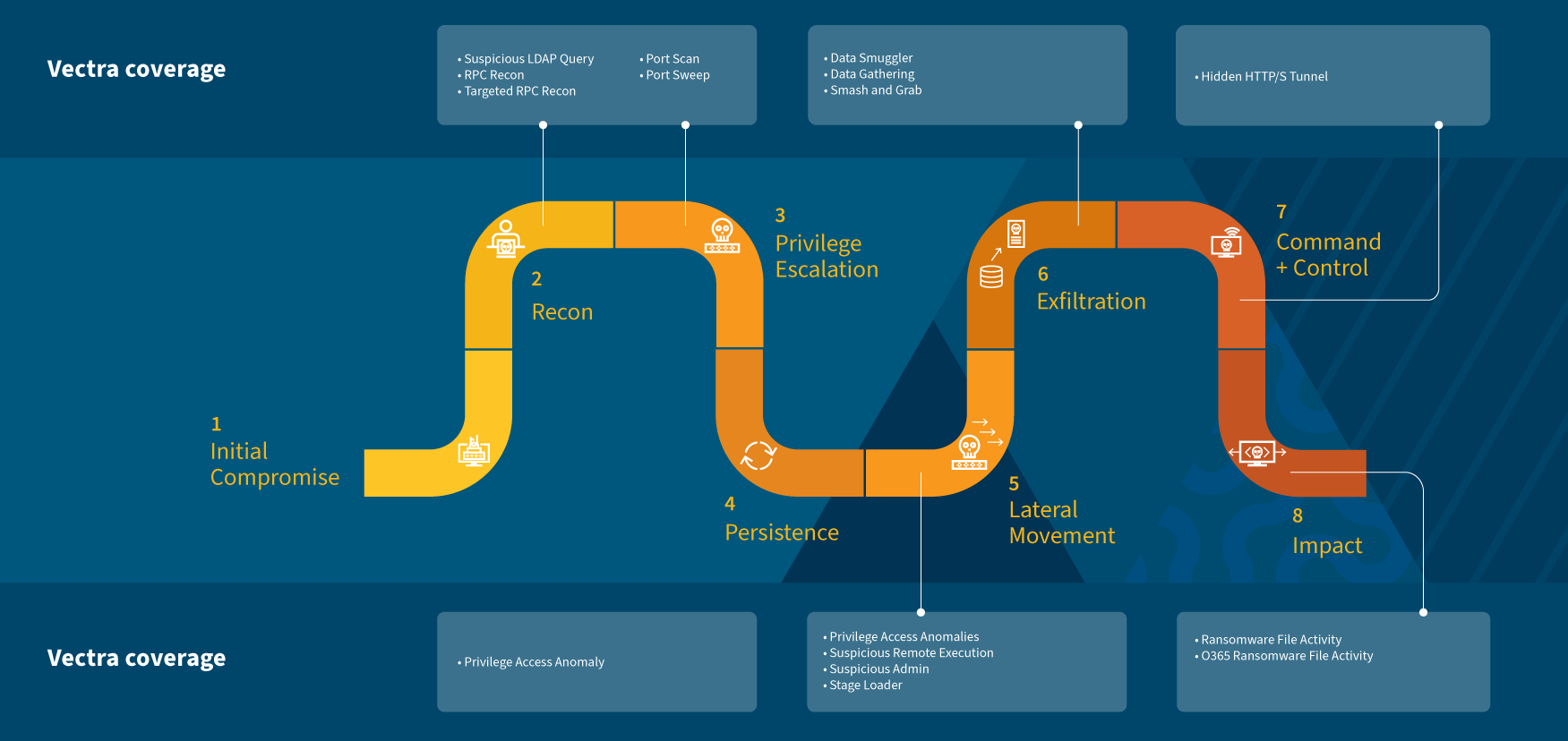
Vectra models detect these threats consistently when seen in the wild because we focus on behaviors, not signatures. Attacker infrastructure, tools change, but behaviors are more stable. This allows Vectra to not just catch the current flavor of ransomware, but newer ones that may be created in the future.
Security operations center (SOC) analysts can leverage the behavioral detections to get ahead of an attacker before the adversary achieves a malicious objective such as exfiltration or encryption of data.
In this blog, I’d like to analyze a typical attack progression from Maze, and how it would appear for someone who was leveraging Vectra to secure their network.
How does a modern Ransomware attack looks like?
Let’s start by looking at a common timeline of a modern ransomware attack:
- Organization is compromised via spear phishing email
- C2 is established
- Executable is dropped and threat actor has long lead time where credential theft and other localized reconnaissance occurs
- Additional tools are downloaded to host such as psexec, Cobaltstrike, Empire, ADFind
- Recon tools executed and results collected
- Threat actor copies payloads to targets in the environment
- Processes are stopped as defensive evasion and encryption takes place
- Ransom note dropped
- Data exfiltration via C2 or TOR
From a SOC perspective, let’s simplify this and distill it into five observable steps.
- Attacker gains a foothold in the targeted company
- Attacker performs reconnaissance in order to find information of interest, or passwords that may enable lateral movement in the network or privilege escalation
- Lateral movement in order to control most hosts
- Exfiltration of sensitive data
- Finally, deployment and execution of Maze ransomware toward the previously created channels
Note that those steps may or may not be present, depending of the actor. As the techniques varies, potential detections listed below cannot be considered certain. Note as well that some people can just open a sample of Maze by accident, infect themselves, which would only trigger ransomware detection, as no interaction within a C2 channel will be performed.
Anatomy of the Maze Ransomware attack
Step 1 - Initial compromise
For initial compromise, some campaigns start with malicious documents, used to launch a cobalt strike instance in order to gain remote control of the “patient zero”. Several cases reported came from a direct compromising, by the actor, using stolen credentials, exploitation of vulnerable software, or weak password on Internet facing devices. The most observed tool used to take control of the patient zero appears to be CobaltStrike.
Step 2 - Recon and privilege escalation
Actors sometimes used privilege escalation in order to be able to execute and deploy the ransomware, move laterally, or discover interesting files. This attack step comprises the reconnaissance behavior.
- This can be done using mimikatz locally.
- The actor can look for files with the word “password” in it, which may trigger file share enumeration.
- Some usage of the enumeration/reconnaissance feature of BloodHound tool have been reported, for the attacker to find hosts of interest, and better understand the target’s architecture.
- Many different tools have been reported for the reconnaissance stage, but they all have the same objective, understand network architecture, places they can move, where to find accounts that may help move further….
- All these behaviors could trigger our recon detections, such as port scan, internal darknet scan, suspicious LDAP query, File share enumeration and so on.
Once the attacker gets a foothold in the target’s environment, several reconnaissance attempts, as well as lateral movement are performed towards other targets.
The screenshot below clearly shows this behavior, IP – 10.50.2.103 being the principal entry point, showing lateral movement and significant reconnaissance behavior.

Step 3 - Lateral movement
For lateral movement itself, attackers mostly leverage Cobalt strike from their initial foothold.
- Some actors create themselves an account on the infected domain. This action could create privilege access anomalies, such as Privilege Anomaly: Unusual Account on Host
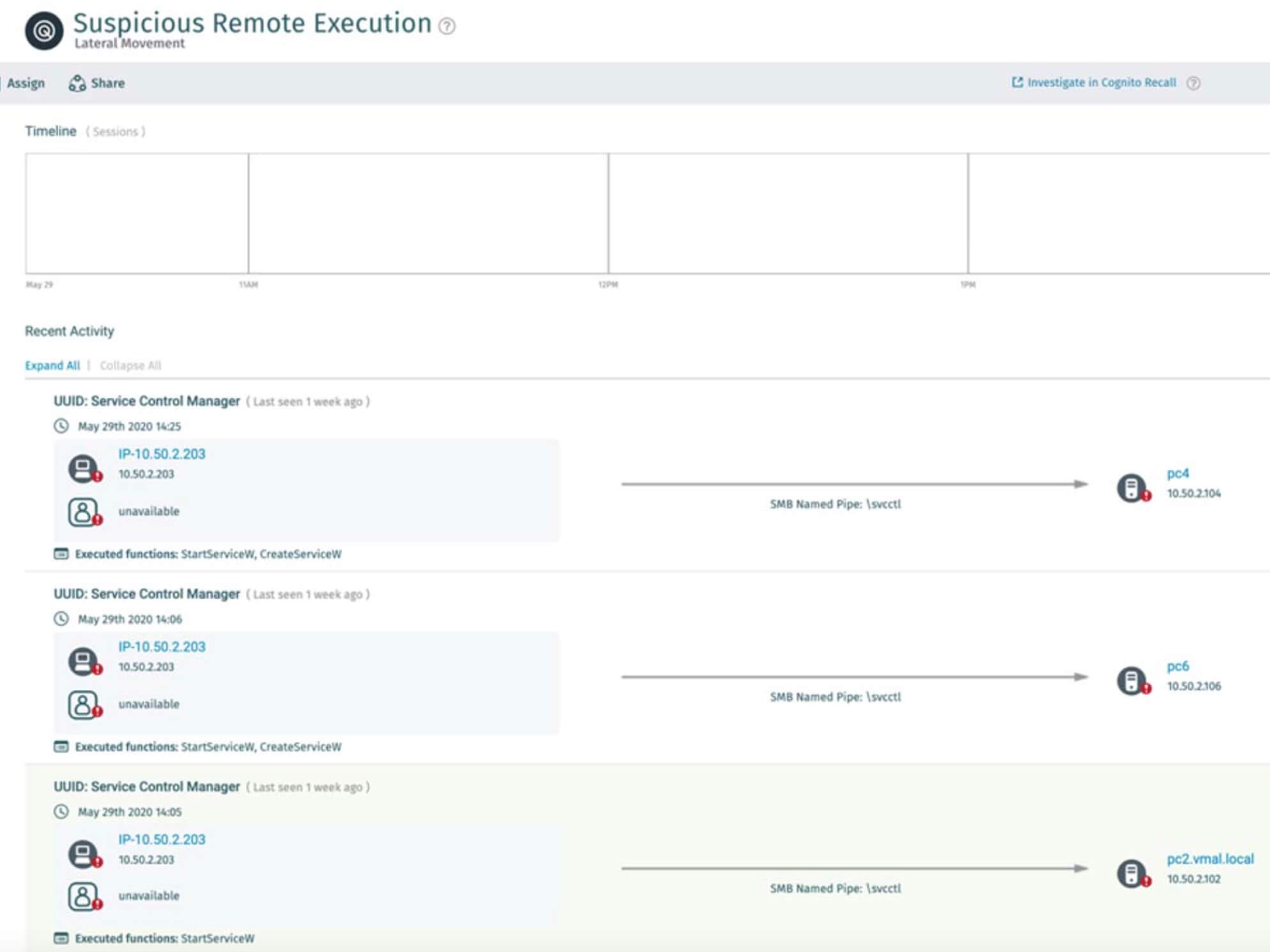
- In case exploitation such as psexec is performed in order to move laterally using the tool, Suspicious Remote Execution is susceptible to fire.
- Some actors used RDP, in this case, Suspicious RDP and RDP Recon detection are susceptible to trigger. One actor has been reported using a tunnel for RDP, which may show as Suspicious Relay, depending on method used by the attacker.
In the Suspicious Remote Execution detail, we see the attacker operating psexec to manage services in neighboring hosts.
Step 4 - Exfiltration
Finally, several cases show exfiltration attempts, prior to encryption by maze, which are done in various manners, mostly towards ftp or cloud hosting services.
- Depending of the volume of exfiltrated files, Data smuggler and Smash and Grab could trigger
- In case the attacker decides to exfiltrate data from a SharePoint site, we can expect “Unusual volume” O365 detection ;)
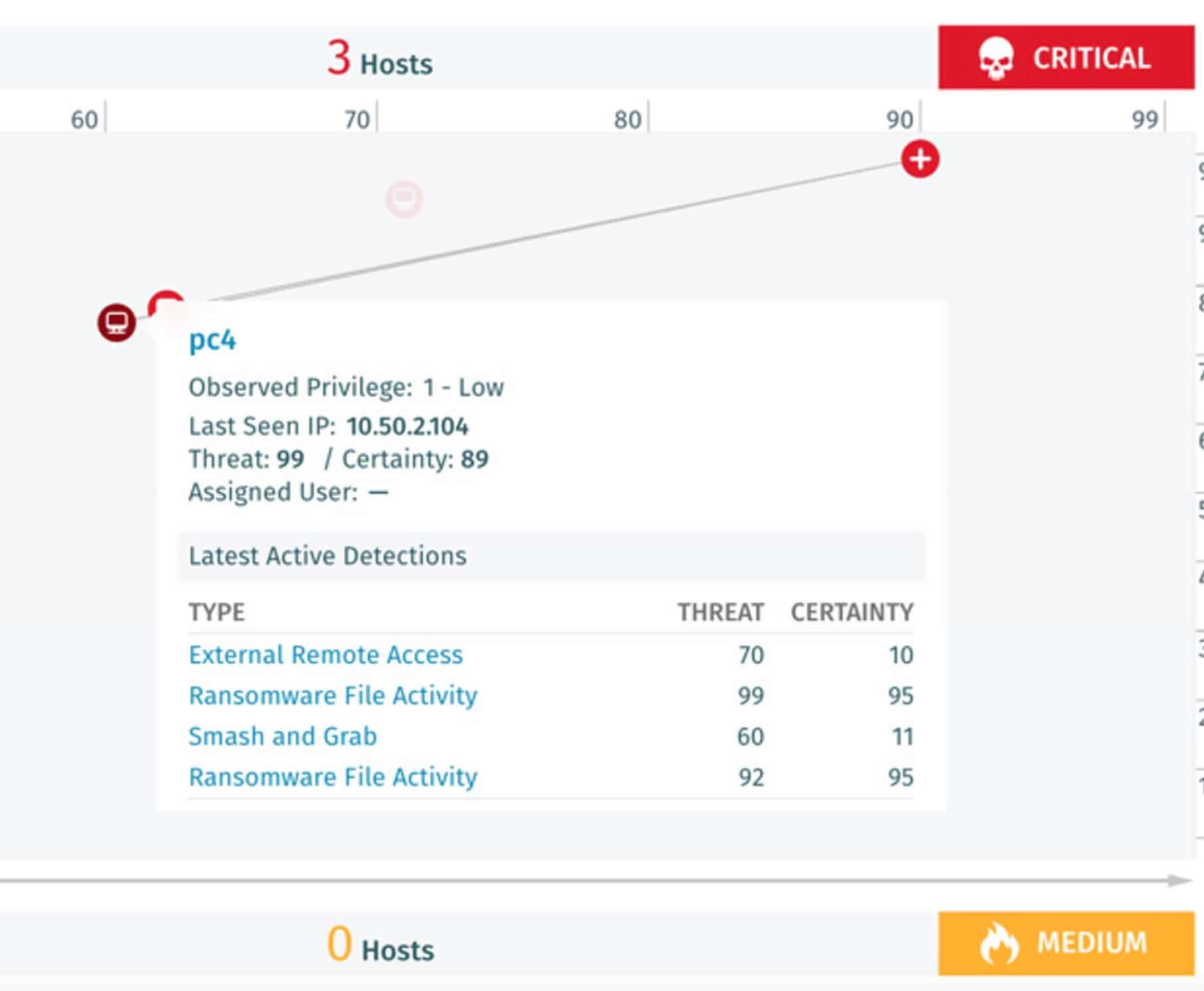
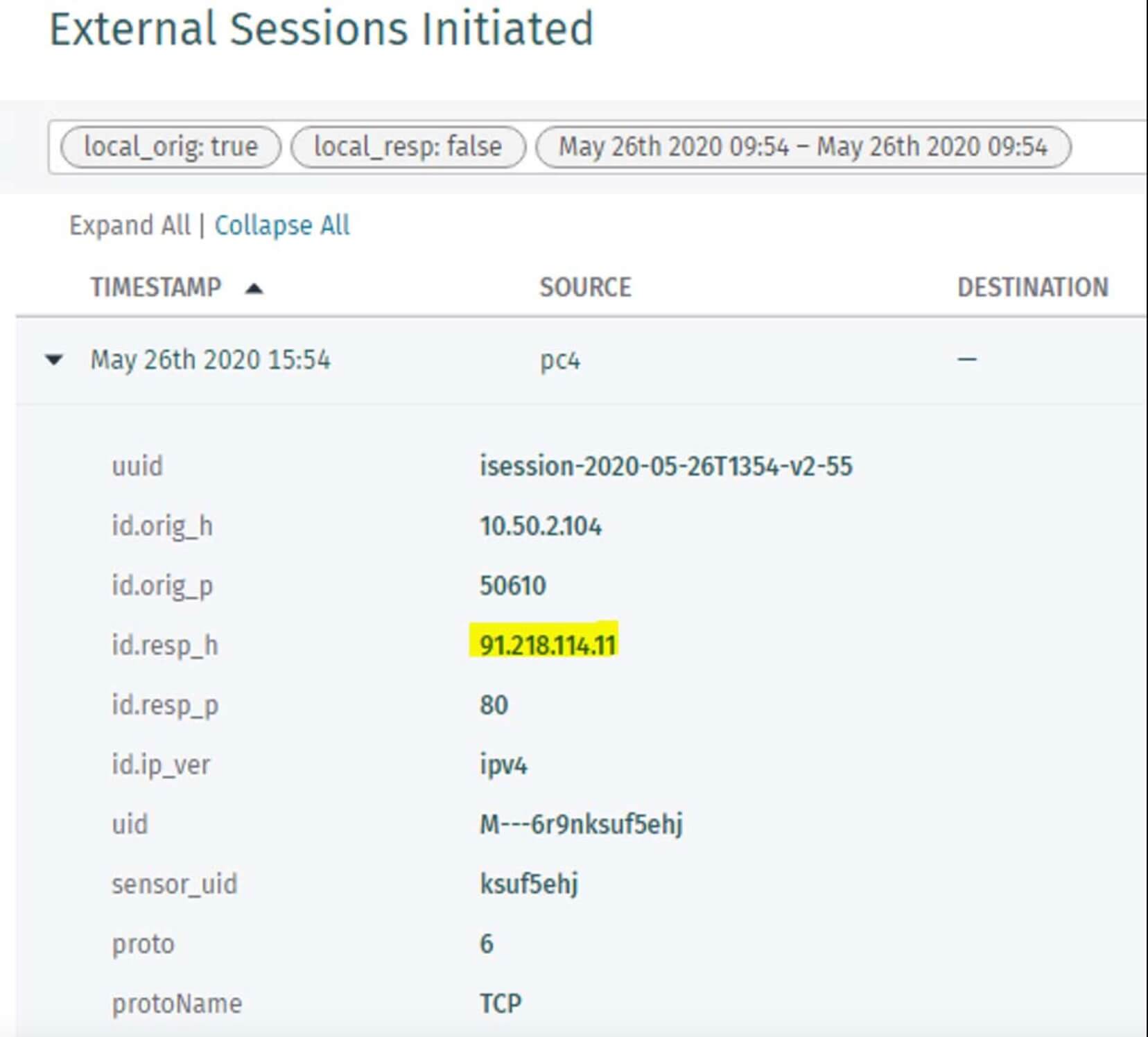
Note here that prior to the detonation of the ransomware itself, the host pc4 suffered external remote access and Smash andGrab exfiltration attempts, which is here part of the exploit chain.
The external remote access is always a strong indicator of an external adversary when combined with reconnaissance detections. In detection detail here you find the type of C2 application, in this case Teamviewer. C2 alerts should always be investigated to rule out threats. Do not rely solely on threat intel but consider the broader scope of activity. Ask yourself:
- Is the host also performing recon?
- Is there suspicious account activity on the host?
- Is the destination logical (in this case an IP in Netherlands)?
- Did endpoint detection and response (EDR) trigger any alerts?

Step 5 - Ransomware
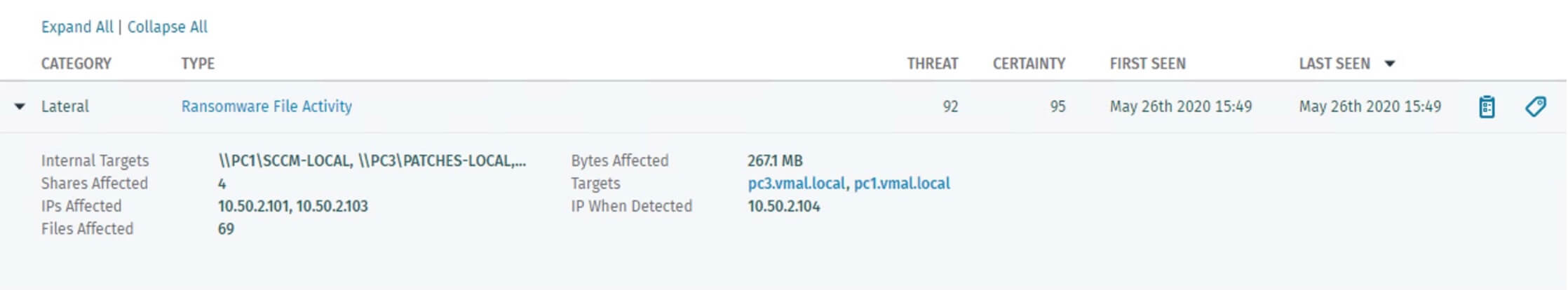
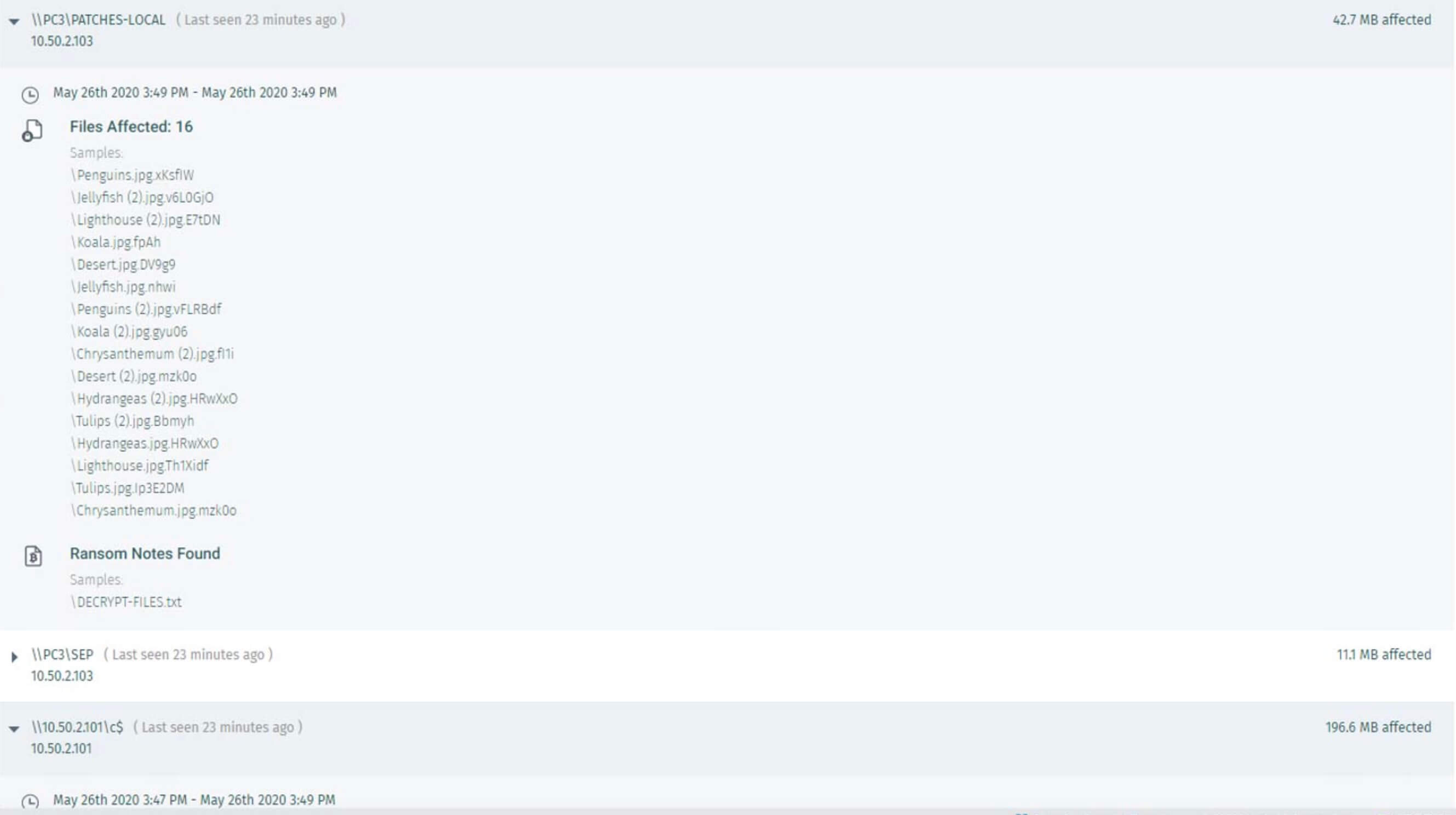
Maze ransomware is then deployed via channels. This one obviously triggers ransomware file activity, as shown below.
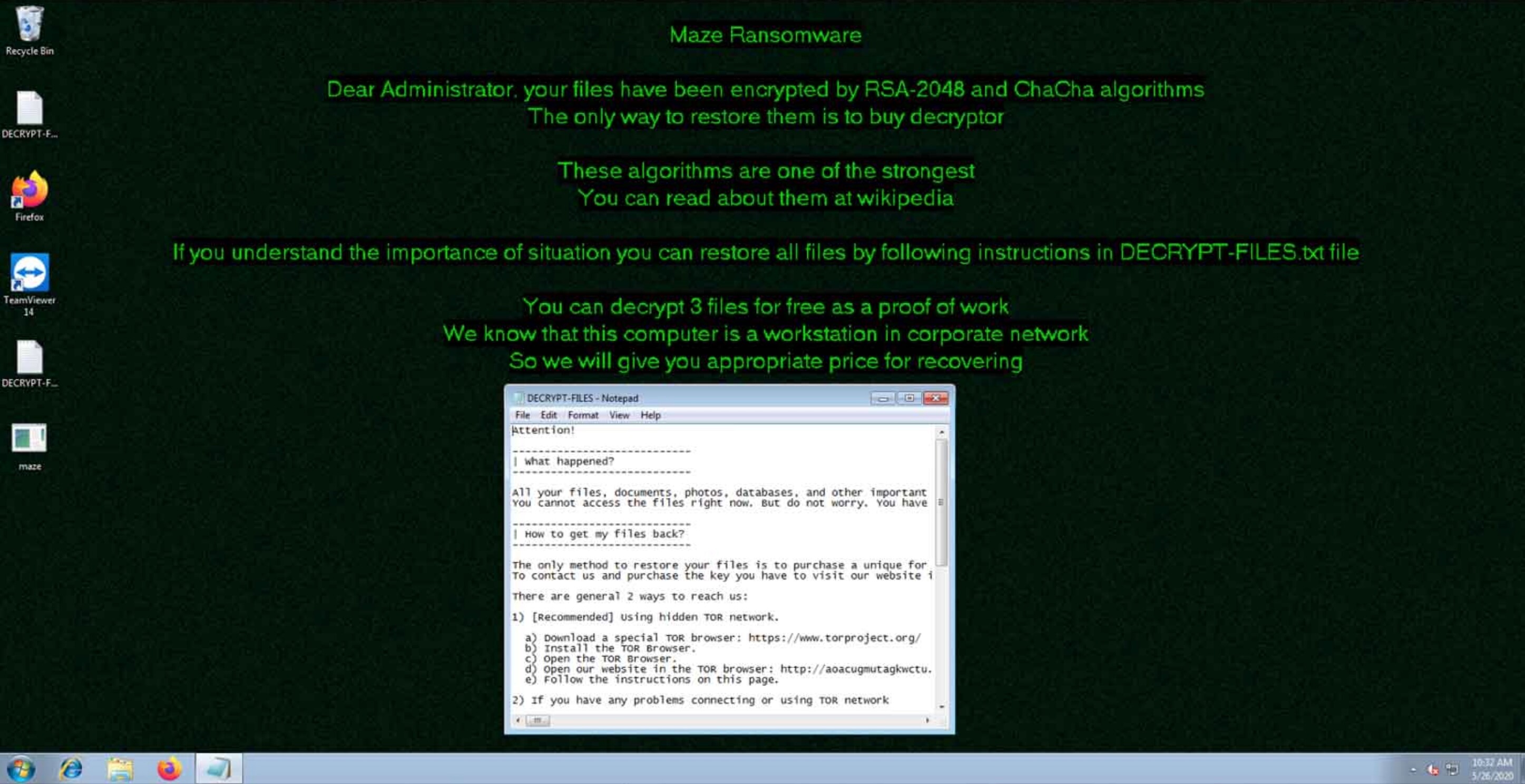
Regarding Ransomware detection itself, the detection view shows the number of files affected, as well as shares names. The ransomware note is also given, as it can help identify certain families of malware by its name:
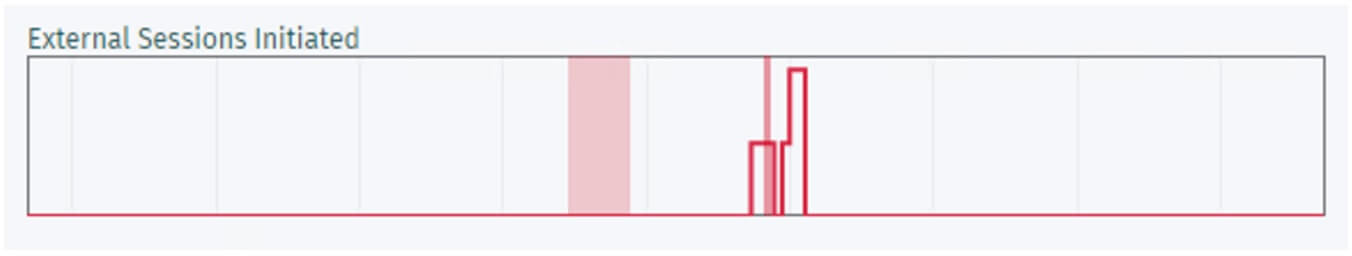
Using Recall enhanced view, we can see clearly that at the time of the attack, some external sessions were launched:
Post Incident Report: 5 Steps to identify an Actual Maze Ransomware attack
Below is a summary of an actual post incident report that shows the steps taken to identify the early indicators of a ransomware attack and prevent the encryption of network file shares.
Vectra has been authorized to publish this post-incident report by ensuring anonymity and protecting the customer’s private data. This type of report is ordinarily kept confidential for internal analysis only.
- Inside the compromised network on Day 1—one week prior to the intended ransomware detonation—the Vectra Consulting Analyst Team detected unmistakable reconnaissance and lateral movement attack behaviors. These phases of the attack lifecycle indicated the attacker was looking for critical systems to compromise before encrypting network file shares for ransom.
- Vectra showed that scans came from a wide range of hosts and other scans were related to ransomware activities as network file shares were enumerated.
- Uncovering additional evidence, Vectra observed that one compromised host was communicating with a known malicious IP address in Ukraine that has been associated with Sodinokibi malware.
- External connections were performed successfully to a Ukraine IP address with a data transfer of about 80 MB.
- The number of detections identified by Vectra was concerning due to the sheer volume of data that was being sent to the outside.
Additional information from the customer linked the attack to Maze ransomware.
Check out this post-incident report, which shows the importance of early cyberattack detection to avert damage and catastrophic data breaches. With certainty and precision, it is vital to identify precursor threat behaviors, swiftly investigate incidents, and arm yourself with the appropriate response tools.
Detect and stop ransomware with Vectra AI
The combination of prioritization of relevant behavior combined with automated response can help detect the threat early and stop it from propagating into the environment. To get in touch with our experts, our newly announced Vectra services enable our customers to mature their security operations and empower them with access to the people at Vectra who are most knowledgeable. And as always, don’t hesitate to contact us to learn more or schedule a demo.







